Climbing into his Volvo, outfitted with a Matrics antenna and a Motorola reader he'd bought on eBay for $190, Chris Paget cruised the streets of San Francisco with this objective: to read the identity cards of strangers, wirelessly, without leaving his car.
It took him 20 minutes to strike hacker's gold.
Zipping past Fisherman's Wharf, his scanner downloaded to his laptop the serial numbers of two pedestrians' electronic U.S. passport cards embedded with radio frequency identification, or RFID, tags. Within an hour, he'd "skimmed" four more of the new, microchipped PASS cards from 20 feet.
Increasingly, government officials are promoting the chipping of identity documents as an application of technology that will help speed border crossings, safeguard credentials against counterfeiters and keep terrorists out of the country.
People are also reading…
But Paget's February experiment showed something privacy advocates had feared for years: That RFID, with other technologies, could make people trackable without their knowledge.
He filmed his heist, and soon his video appeared on the Web, intensifying a debate over a push by governments, federal and state, to put tracking technologies in ID documents and over their potential to erode privacy.
Putting a traceable RFID in every pocket could make everybody a blip on someone's radar screen, critics say, and redefine Orwellian government snooping for the digital age.
"Little Brother," some are already calling it, even though elements of the global surveillance web they warn against exist only on drawing boards, neither available nor approved for use.
But with advances in tracking technologies coming at an ever-faster rate, critics say, it won't be long before governments could be able to identify and track anyone, anywhere, in real time.
On June 1, it became mandatory for Americans entering the United States by land or sea from Canada, Mexico, Bermuda and the Caribbean to present identity documents with RFID tags, though conventional passports remain valid until they expire.
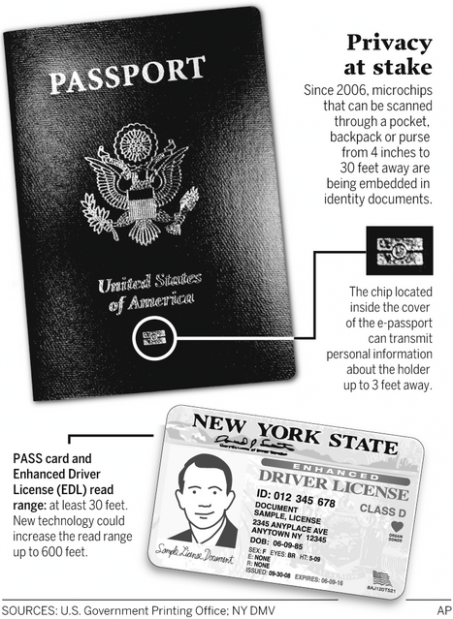
Among new options are the chipped "e-passport," and the new, electronic PASS card — credit-card-sized, with the bearer's digital photo and a chip that can be scanned through a pocket or purse from 30 feet.
Alternatively, travelers can use "enhanced" driver's licenses embedded with RFID tags now being issued in some border states: Washington, Vermont, Michigan and New York. Texas and Arizona have entered into agreements with the federal government to offer chipped licenses, and the U.S. Department of Homeland Security has recommended expansion to non-border states.
The purpose of using RFID is not to identify people, says Mary Ellen Callahan, the chief privacy officer at Homeland Security, but "to verify that the identification document holds valid information about you."
An RFID document that doubles as a U.S. travel credential "only makes it easier to pull the right record fast enough, to make sure that the border flows and is operational" — even though a 2005 Government Accountability Office report found that government RFID readers often failed to detect travelers' tags.
Critics warn that RFID-tagged IDs will enable identity thieves and other criminals to commit "contactless" crimes against victims who won't know they've been violated.
Neville Pattinson, vice president for government affairs at Gemalto Inc., a major supplier of microchipped cards, is no RFID basher. He's a board member of the Smart Card Alliance, an RFID industry group, and is serving on Homeland Security's Data Privacy and Integrity Advisory Committee.
In a 2007 article in a newsletter for privacy professionals, Pattinson called the chipped cards vulnerable "to attacks from hackers, identity thieves and possibly even terrorists."
RFID, he wrote, has a fundamental flaw: Each chip is built to transmit its unique identifier "in the clear, exposing the tag number to interception during the wireless communication."
Once a tag number is intercepted, "it is relatively easy to directly associate it with an individual," he said. "If this is done, then it is possible to make an entire set of movements posing as somebody else without that person's knowledge."